SSO requires a Business or Enterprise plan. View plans
How SSO Works in Invent
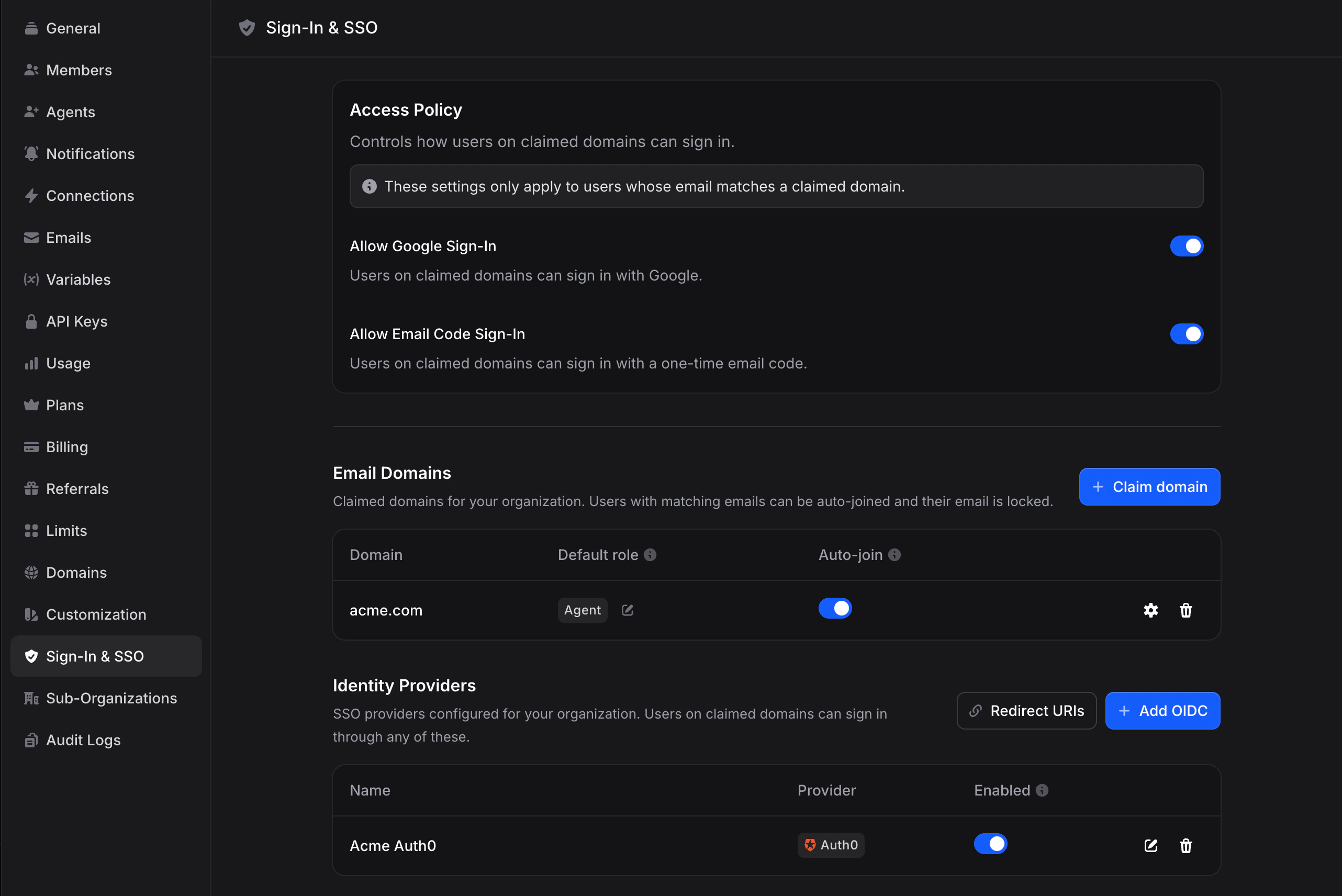
SSO in Invent is built on three pieces that work together:Access Policy
Org-wide rules for which login methods (SSO, Google, email code) are allowed for users on your verified domains.
Domains
Email domains your organization has claimed and verified. Controls auto-join, default roles, and profile sync for users who sign up with a matching email.
Profiles
Identity provider configurations (Okta, Entra ID, Google, etc.). Each profile is an OIDC connection your users can sign in through.
Key Concepts
Verified Domains
A domain is an email domain you’ve proven your organization owns (for example,acme.com). Verification happens through a one-time 6-digit code sent to an address on that domain. A domain can only be claimed by one organization in Invent. The first org to verify wins.
SSO Profiles
A profile is the OIDC configuration for one identity provider. You can have multiple profiles in the same org, for example one for your main workforce IdP and another for a contractor IdP. Invent automatically recognizes popular vendors by their issuer URL and shows the matching logo and name.Just-in-Time (JIT) Provisioning
When a user signs in through SSO for the first time and no Invent account exists, Invent creates one automatically. You can disable this per-profile if you’d rather invite users explicitly.Auto-Join
When a new user signs up with an email matching a verified domain, they can be automatically added to your organization as a member with a default role you set. This applies to all sign-in methods, not just SSO. Someone invited to Invent through Google sign-in using their@acme.com email would still be auto-joined.
Profile Sync
On every SSO sign-in, Invent can refresh the user’s name, avatar, and email from the IdP. This keeps identity data in sync with your directory of record and optionally locks users out of editing it themselves.Who Can Manage SSO
SSO management requires:- Admin role in the organization
- Business or Enterprise plan
What End Users See
Users on your verified domains get a clean, branded sign-in experience:- They visit the Invent sign-in page and click Use SSO instead.
- They enter their company email and click Sign in with SSO.
- Invent looks up your SSO configuration and redirects them to your IdP.
- After authenticating with your IdP, they’re signed in to Invent.
Plan Limits
| Feature | Pay As You Go | Business | Enterprise |
|---|---|---|---|
| SSO Domains | ✗ | 5 | 50 |
| SSO Profiles | ✗ | 5 | 50 |
| OIDC Providers | ✗ | ✓ | ✓ |
| Access Policy | ✗ | ✓ | ✓ |
| Session TTL Control | ✗ | ✓ | ✓ |
Setup Checklist
Ready to roll out SSO? Follow this order:Verify your domain
Claim and verify the email domain your team uses (e.g.
acme.com). You’ll receive a 6-digit code by email.Configure your identity provider
Create an OIDC application in your IdP. Copy Invent’s Redirect URIs into your IdP’s allowed redirect list.
Create an SSO profile
Add a profile in Invent with your IdP’s Issuer URL, Client ID, and Client Secret. Invent auto-discovers the rest from your IdP’s
.well-known endpoint.Test the sign-in flow
Sign out and sign in again using your company email. You should see your IdP in the SSO picker.
Tune your access policy
Once SSO works end-to-end, decide whether to keep Google and email-code sign-in on or require SSO exclusively for your domain.
Supported Identity Providers
Invent speaks standards-compliant OpenID Connect (OIDC), so it works with any OIDC-capable IdP. We have first-class display recognition (name + logo) for:- Microsoft Entra ID (formerly Azure AD)
- Google Workspace
- Okta
- Auth0
- PingOne / Ping Identity
- OneLogin
- JumpCloud
- Amazon Cognito
- IBM Security Verify
- Oracle Identity Cloud Service
- Cisco Duo
SAML 2.0 is on the roadmap but not yet supported for sign-in. If your IdP only speaks SAML, reach out. We can often expose an OIDC endpoint on the same IdP.