SSO Profiles require a Business or Enterprise plan. View plans

The Profiles Table
| Column | Description |
|---|---|
| Name | The label you gave this profile (e.g. “Acme Okta”) |
| Provider | Vendor badge, auto-detected from the Issuer URL (Okta, Entra ID, etc.) or “OIDC” |
| Enabled | Toggle. When off, this profile is hidden from the sign-in picker |
| Actions | ✏️ Edit • 🗑️ Delete |
Before You Start
Two things to prepare before creating the profile in Invent:- An OIDC application in your IdP (Okta, Entra ID, etc.). You’ll get three values:
- Issuer URL: the base URL of your IdP (e.g.
https://acme.okta.com) - Client ID: identifier for the OIDC app
- Client Secret: secret credential for the OIDC app
- Issuer URL: the base URL of your IdP (e.g.
- Invent’s Redirect URIs registered on that application. See below.
Redirect URIs
Your IdP needs to know which URLs it’s allowed to send users back to after authentication. In Invent, click the 🔗 Redirect URIs button on the Profiles section to see the full list for your workspace.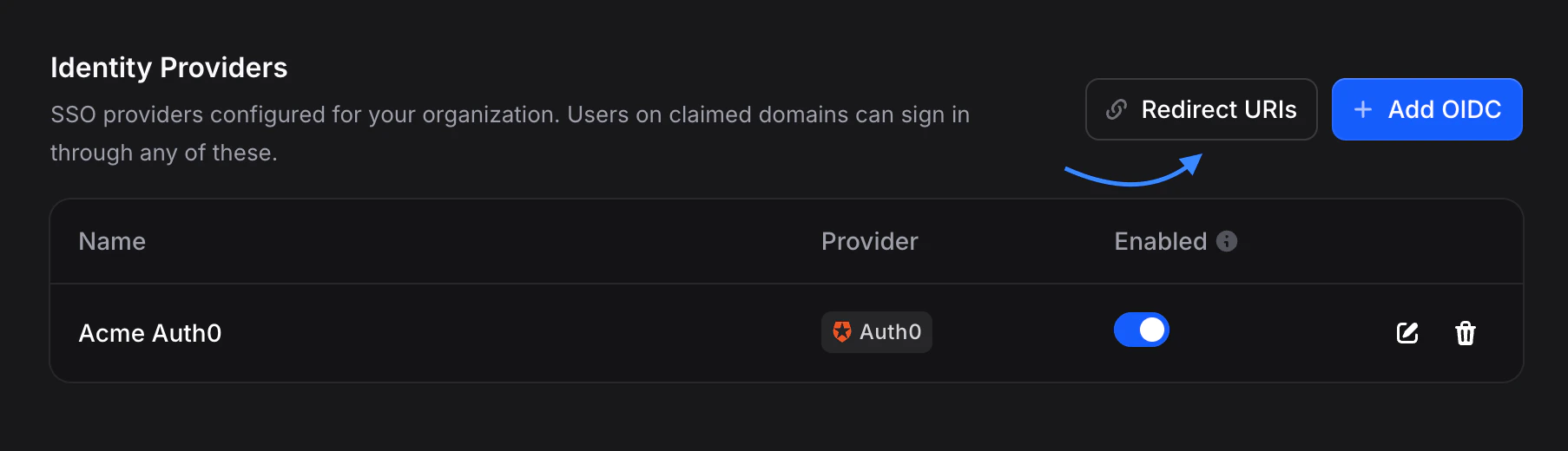
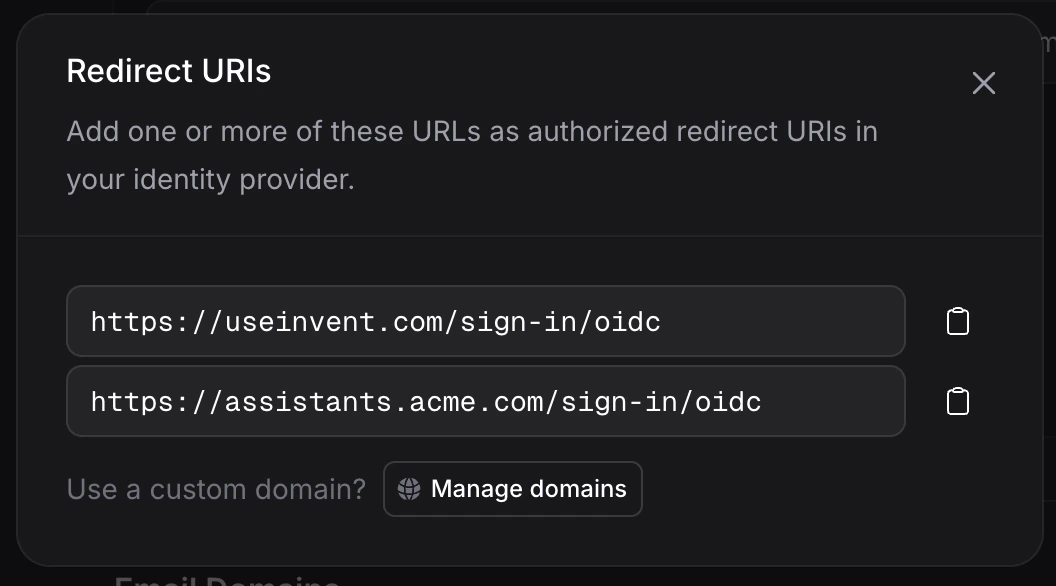
/sign-in/oidc redirect URI. No extra configuration is needed inside Invent, but every URI in the dialog must be registered in your IdP so users on any of your hostnames can complete the sign-in flow.
The Manage domains button in the Redirect URIs dialog jumps you straight to Settings → Domains where you can add a new custom domain. As soon as it’s verified, it shows up as a new redirect URI here.
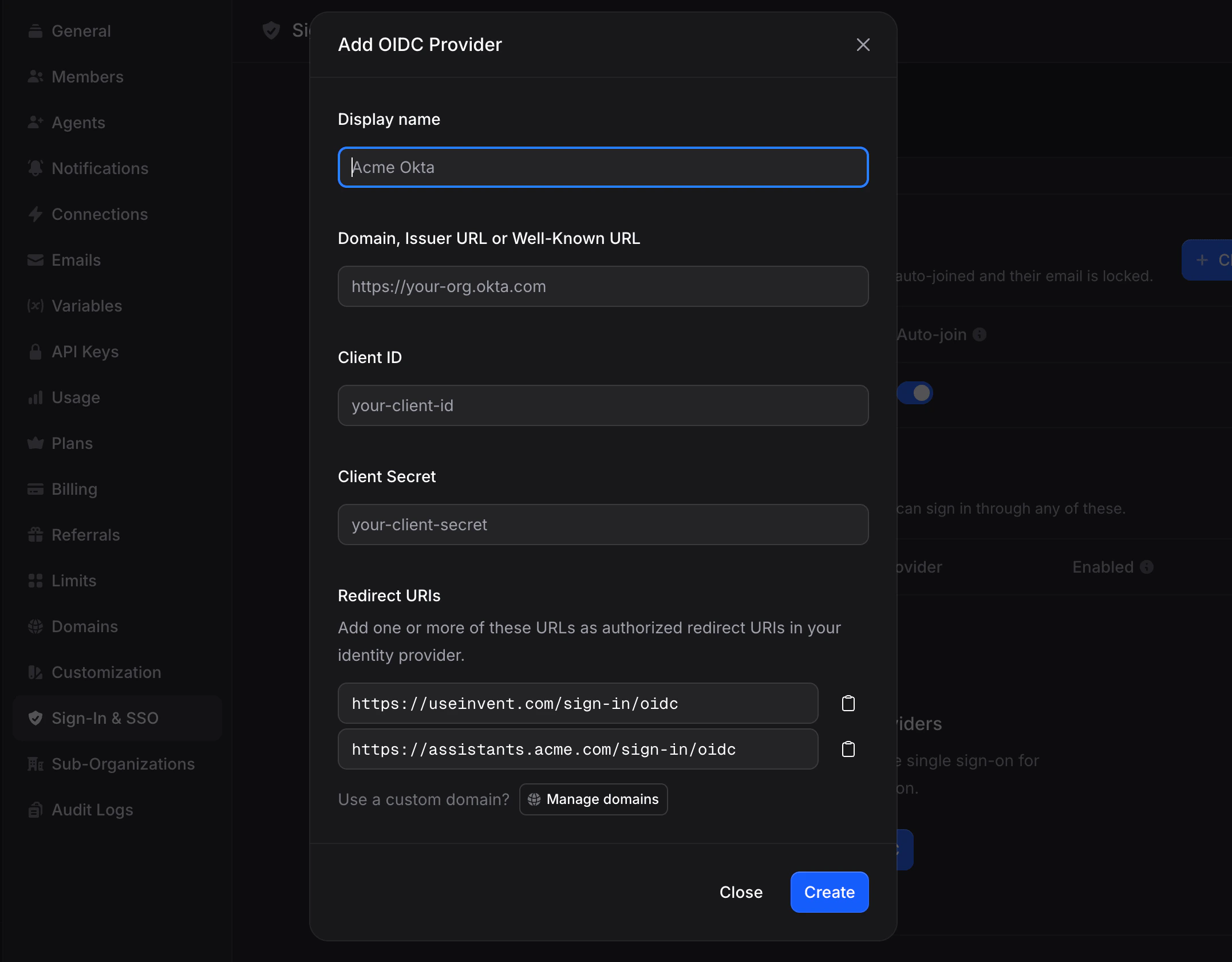
Creating a Profile
- Go to Settings → SSO → Profiles.
- Click + Add Profile.
- Fill in the form:
- Name: a friendly label shown in the sign-in picker (e.g. “Acme Okta”).
- Domain, Issuer URL, or Well-Known URL: enter your IdP base URL. You can paste the full
.well-known/openid-configurationURL and Invent will normalize it. - Client ID: from your IdP.
- Client Secret: from your IdP.
- Click Create.
Issuer URL Examples
| IdP | Issuer URL format |
|---|---|
| Okta | https://acme.okta.com |
| Microsoft Entra ID | https://login.microsoftonline.com/<tenant-id>/v2.0 |
| Google Workspace | https://accounts.google.com |
| Auth0 | https://acme.auth0.com |
| PingOne | https://auth.pingone.com/<env-id>/as |
| OneLogin | https://acme.onelogin.com/oidc/2 |
| JumpCloud | https://oauth.id.jumpcloud.com/ |
| Amazon Cognito | https://cognito-idp.<region>.amazonaws.com/<pool-id> |
| IBM Security Verify | https://<tenant>.verify.ibm.com/oidc/endpoint/default |
| Oracle IDCS | https://<tenant>.identity.oraclecloud.com |
| Cisco Duo | https://<tenant>.duosecurity.com |
OIDC Scopes
Invent requests these standard OIDC scopes from your IdP:openid, email, profile. Your IdP admin doesn’t need to configure anything special. These are the default scopes every OIDC provider supports.
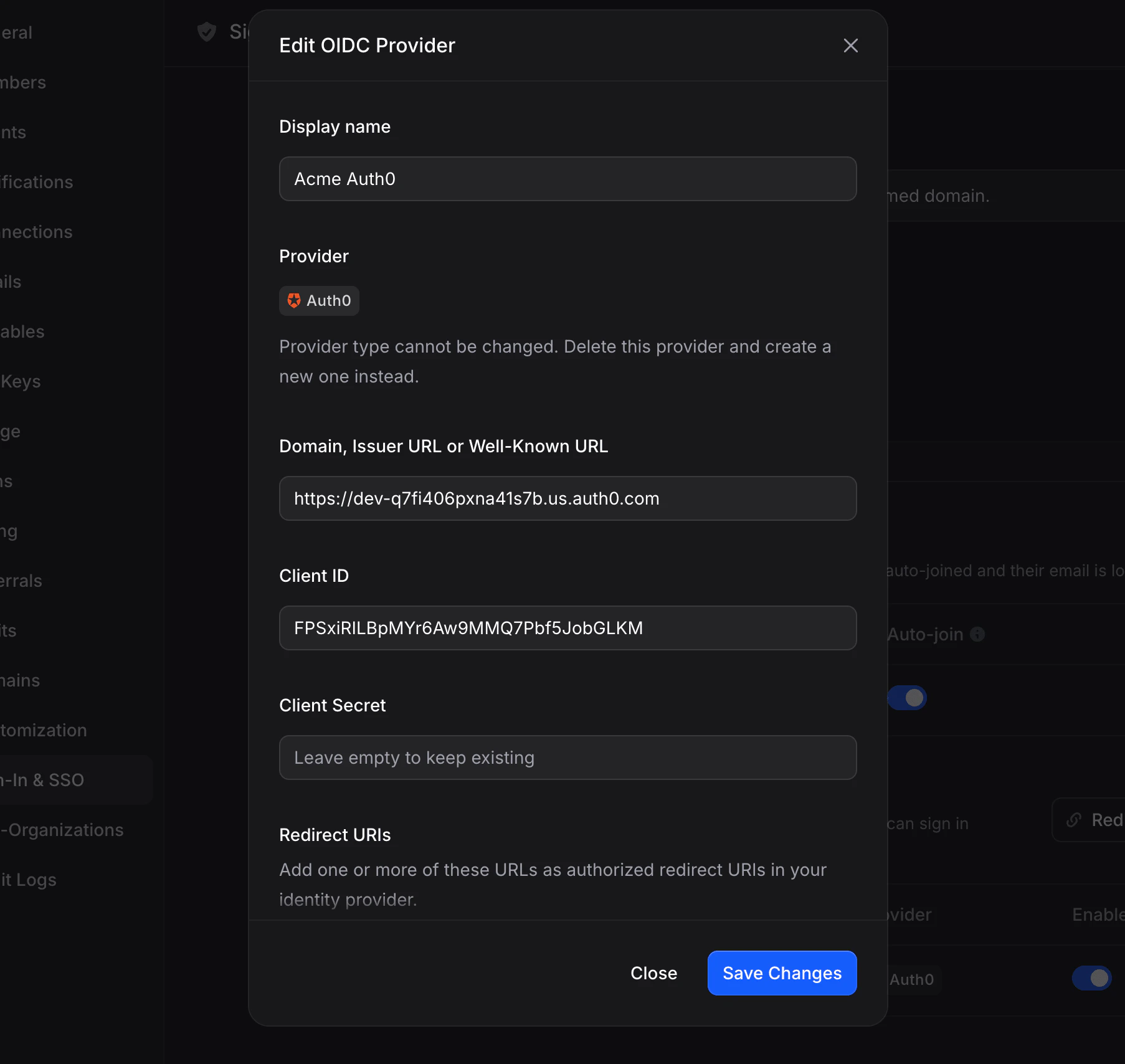
Editing a Profile
Click the ✏️ Edit icon on any profile row to update it.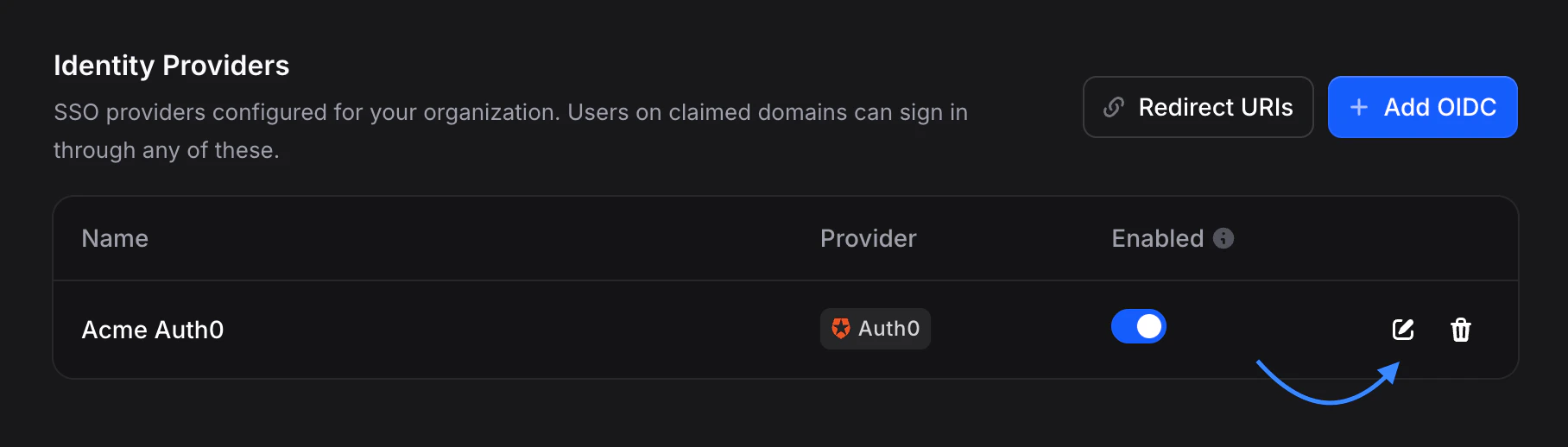
- Name
- Issuer URL / Client ID, for example when you rotate or recreate the OIDC app in your IdP
- Client Secret. Leave blank to keep the existing secret; enter a new value to rotate
The provider type (OIDC) cannot be changed on an existing profile. If you need a different protocol, delete the profile and create a new one.
Enabling & Disabling Profiles
Flip the Enabled toggle on a profile row to pause it without deleting anything.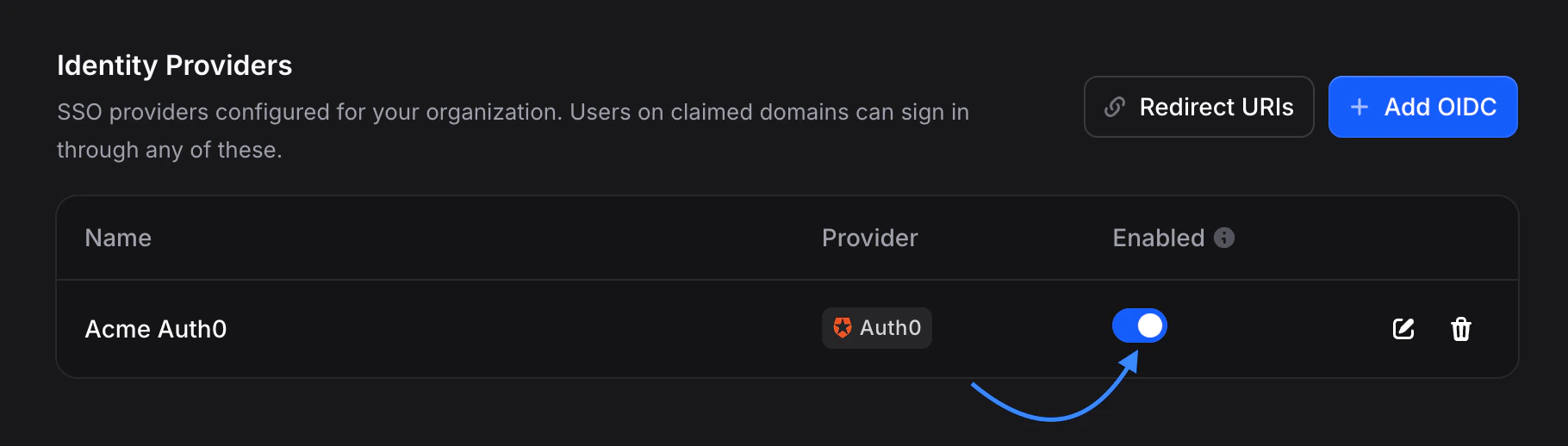
- Is hidden from the sign-in picker
- Rejects any in-flight OIDC callbacks
- Keeps existing sessions (they’re not revoked)
- Retains all configuration, so you can re-enable it instantly
Deleting a Profile
Click the 🗑️ Delete icon to remove a profile. Deletion is protected by a confirmation dialog that tells you how many active sessions the profile currently has.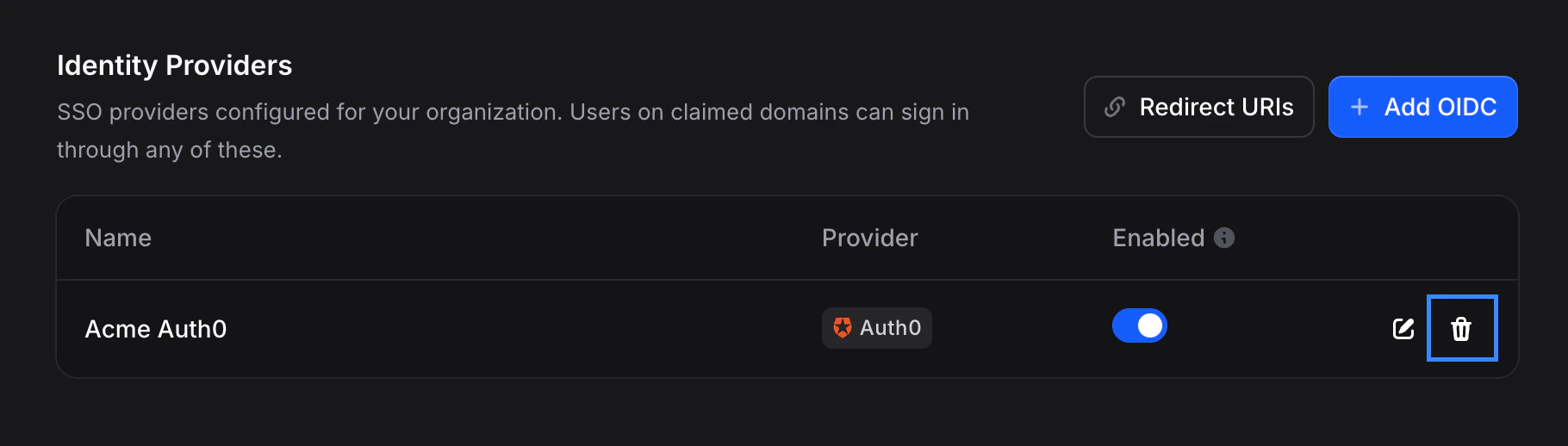
JIT (Just-in-Time) Provisioning
When a user signs in through SSO for the first time, Invent needs to decide whether to create a new account on the fly or reject the sign-in:- JIT enabled (default): first-time SSO sign-ins auto-create the Invent user. Combined with Auto-Join on the domain, this is the fastest way to onboard a team at scale.
- JIT disabled: first-time SSO sign-ins are rejected with a message asking the user to get invited first. Use this when you want explicit control over who gets provisioned.
Revoking Sessions
Dedicated session revocation (a sessions table with per-user sign-out and “sign out everyone” controls) is coming soon. For now, deleting a profile is the only way to revoke its direct SSO sessions, and that happens automatically as part of the delete.
Vendor Detection
Invent recognizes popular IdPs from the hostname of your Issuer URL and shows the right logo and name automatically. This is display-only. The authentication pipeline is standards-compliant OIDC regardless of the detected vendor. Supported vendors:| Vendor | Matches on hostname |
|---|---|
| Microsoft Entra ID | login.microsoftonline.com |
accounts.google.com | |
| Okta | *.okta.com, *.oktapreview.com |
| Auth0 | *.auth0.com |
| PingOne | *.pingone.com |
| Ping Identity | *.pingidentity.com |
| OneLogin | *.onelogin.com |
| JumpCloud | *.jumpcloud.com |
| Amazon Cognito | *.amazoncognito.com, cognito-idp.*.amazonaws.com |
| IBM Security Verify | *.appid.cloud.ibm.com, *.verify.ibm.com |
| Oracle IDCS | *.identity.oraclecloud.com |
| Cisco Duo | *.duosecurity.com |
auth.acme.com), your profile still works. It’ll just display as a generic OIDC connection without a vendor logo.
Security
- Client secrets are encrypted at rest using Invent’s secret management, and never leave the backend in plaintext. The Invent UI and API read a public-config view that omits the secret.
- OIDC discovery is cached for 10 minutes. When you change the Issuer URL, the cache is invalidated automatically.
- Email verification is enforced: if your IdP returns
email_verified: falsein the ID token, Invent rejects the sign-in. emailfallback topreferred_username: some tenants of Entra ID don’t emitemailin ID tokens. Invent falls back topreferred_username(an email-formatted UPN) when needed.
Troubleshooting
'Could not reach the OIDC issuer'
'Could not reach the OIDC issuer'
Invent couldn’t fetch the
.well-known/openid-configuration document from your Issuer URL. Verify the URL is correct, publicly reachable, and uses HTTPS. Private-network IdPs aren’t supported.'The identity provider rejected the credentials'
'The identity provider rejected the credentials'
The Client ID or Client Secret is wrong or the secret was rotated. Re-enter both in the Edit dialog.
'The sign-in attempt has expired or already been used'
'The sign-in attempt has expired or already been used'
Each sign-in attempt is single-use and valid for 10 minutes. Ask the user to start the sign-in flow again from the Invent sign-in page.
'The email is not on a domain claimed by this organization'
'The email is not on a domain claimed by this organization'
SSO only accepts users whose email matches a verified domain on the same org. Add the user’s domain to SSO domains first, or have them use a different email.
'The identity provider returned an unverified email address'
'The identity provider returned an unverified email address'
The user’s email isn’t verified in your IdP. Have them complete email verification in the IdP first, or adjust your IdP’s claim settings.
'Automatic member provisioning is disabled for this SSO profile'
'Automatic member provisioning is disabled for this SSO profile'
JIT is off on this profile and the user has no pre-existing Invent account. Invite them first, or enable JIT.